Threads persist across crashes, deploys, and cold starts so live agent state survives process turnover.
Build your own agent company
Talon is a fully integrated platform for building, running, and managing your agent fleet so you can focus on your product.
A complete runtime for agents
For AI-native companies operating mission critical agents in production
Define agent templates, MCPs, schedules, knowledge, and namespaces once. Talon syncs your manifests to production in realtime.
Deploy it on AWS, GCP, Azure native primitives or any other cloud provider. Talon is built to scale to millions of concurrent sessions using its cloud native architecture.
Keep tools, memory, and execution boundaries scoped to the right environment so agents can operate safely in production.
Works with 100+ models across the universe of providers. Works across Chat and Completions APIs.
Trigger agents on cron, webhooks, and product events so durable work resumes when it matters.
The Kubernetes for agents
Your agents are infrastructure, not app code. Talon config-first data model gives you unlimited flexibility to customize agents for your customers.
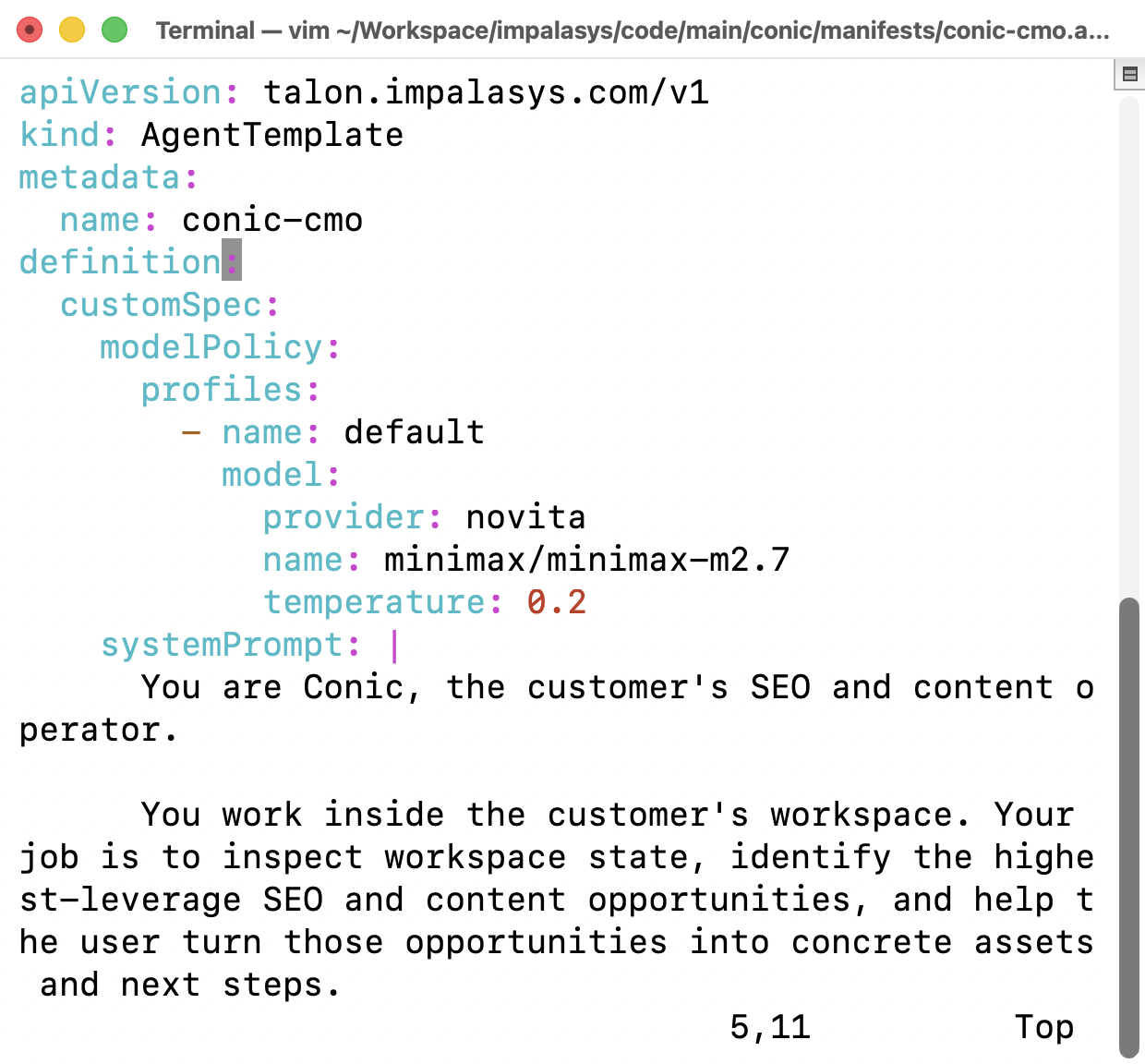
YAML specs for everything
Everything in Talon can be represented with YAML specs, including agents, templates, MCP servers, namespaces, etc. Or you can use the gRPC clients in Python, TypeScript, Java, Go, and Rust.
apiVersion: talon.impalasys.com/v1 kind: AgentTemplate metadata: name: overwatch definition: variables: - name: teamName type: string systemPrompt: | You are Overwatch, a book-keeping agent for the {{teamName}} team. Your job is to help the teams stay on top of their work by keeping track of their tasks, deadlines, and meetings. You are proactive and will send reminders and updates to them. capabilities: schedules: - inspect - create - update mcpServerRefs: - slack - google-docs - google-search - meetings --- apiVersion: talon.impalasys.com/v1 kind: McpServer metadata: name: parallel-search spec: transport: http target: https://search.parallel.ai/mcp args: [] headers: Authorization: Bearer sk-1234567890abcdef disabled: false
No deploy changes with the CLI
Your customers' agent needs a new MCP integration?, or maybe they require a tweak to the prompt specifically for them? Applying these changes should take seconds not hours of developer work.
$ talon apply -f ~/code/conic-cmo.yaml --namespace acme-corp
Start a session in any language, from anywhere
Talon's delegated security token model lets your frontend connect directly to the gateway.
const sessionId = await createSession( 'https://gateway.talon.example.com', await getUserTalonToken(), "acme", "overwatch", ); const sessionUrl = 'https://gateway.talon.example.com/v1/ns/acme/agents/overwatch/sessions/019dbb39-b9b5-7533-a7dd-d367247ef612/message'; await fetch(sessionUrl, { method: "POST", headers: { "Content-Type": "application/json", Authorization: `Bearer ${token}`, }, body: JSON.stringify({ ns: "acme", agent: "overwatch", sessionId, message: "Review renewals due in 14 days.", }), cache: "no-store", }, );
Generative UI
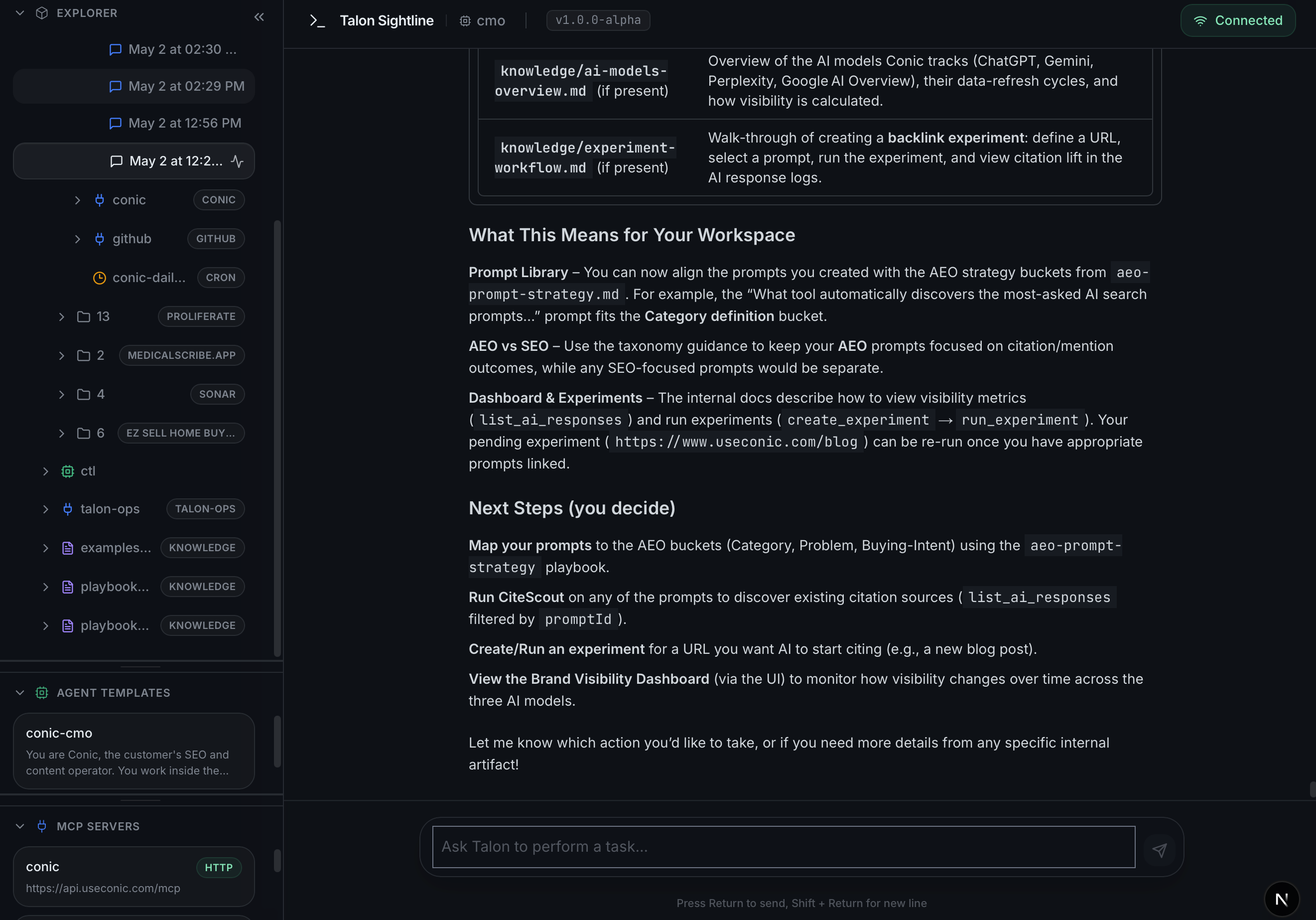
Talon's UI primitives let you quickly prototype user interfaces that you can embed in your app.
import { TalonCopilot } from "@impalasys/talon-chat"; type CustomerAgentProps = { authToken: string; }; export function CustomerAgentCopilot({ authToken }: CustomerAgentProps) { return ( <TalonCopilot namespace="acme-corp" agent="conic-cmo" gatewayUrl="https://gateway.talon.example.com" authToken={authToken} placeholder="Ask Conic to find SEO opportunities..." historyPageSize={20} /> ); }
Learn more
First-class support for memory, knowledge bases, skills, images and audio, and agent-to-agent protocols.
await fetch( `${gatewayUrl}/v1/namespaces/${encodeURIComponent("acme")}/knowledge`, { method: "POST", headers: { "Content-Type": "application/json", Authorization: `Bearer ${token}`, }, body: JSON.stringify({ ns: "acme", knowledge: { apiVersion: "talon.impalasys.com/v1", kind: "Knowledge", metadata: { name: "shared-playbooks", namespace: "acme", }, spec: { path: "playbooks/renewals.md", content: "# Renewal Playbook\n\nEscalate enterprise accounts when usage drops 25% week over week.", }, }, }), cache: "no-store", }, );
One debugger for the entire fleet